Mail Us For Support
Office Address
Chennai, TN, INDIA
PROFESSIONAL IT SERVICE & SOLUTIONS IN INDIA
PROFESSIONAL IT SERVICE & SOLUTIONS IN INDIA
Mail Us For Support

Are you looking for a reliable and experienced company to develop a customized BPM (Business Process Management) application to streamline your business operations? Look no further than our company with 18 years of experience in BPM application development!
We understand that every business has unique processes and requirements, and we specialize in creating tailor-made BPM solutions that fit your specific needs. Our team of expert developers and analysts work closely with you to identify pain points and areas for improvement in your current processes, and design an application that optimizes your workflow and increases efficiency.
Our BPM applications are built using the latest technologies and industry best practices, ensuring that your business stays ahead of the curve and has a competitive edge in your industry. We provide end-to-end services, from consultation and design to development, testing, and deployment, ensuring that your BPM application is fully integrated and functional.
We also offer ongoing support and maintenance services to ensure that your BPM application remains up-to-date and meets the changing needs of your business. Our team is available to answer any questions or concerns you may have, and we are committed to delivering high-quality solutions that exceed your expectations.
Investing in a customized BPM application is an investment in the future of your business. Let our experienced team help you optimize your processes and maximize your productivity. Contact us today to learn more about our BPM application development services!
we specialize not only in BPM (Business Process Management) application development but also in the integration of IoT (Internet of Things) technologies to create intelligent and automated BPM solutions.
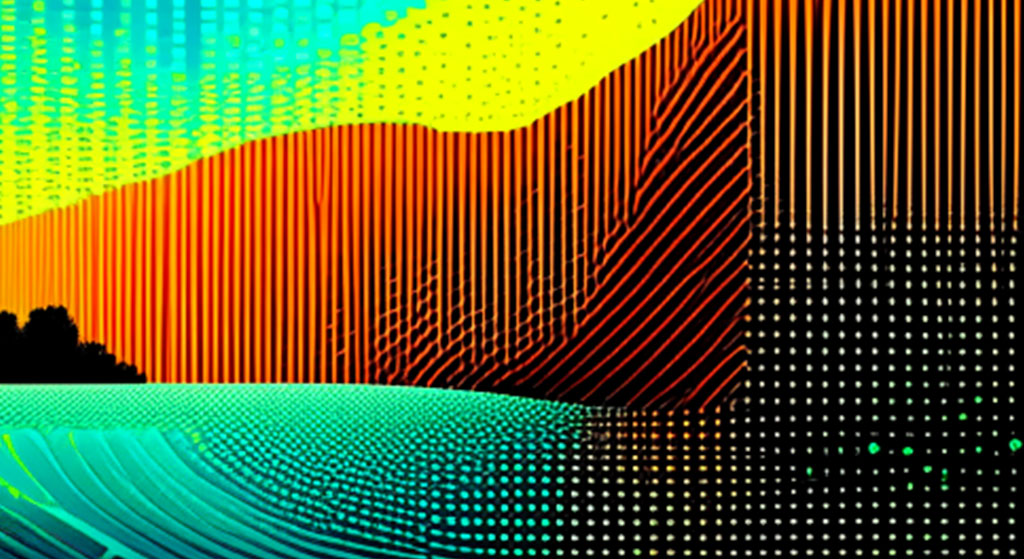
Our IoT-powered BPM applications leverage sensors, devices, and data to monitor and control physical processes, enabling you to optimize and automate your business operations. Our team of experienced developers and analysts work closely with you to identify areas where IoT can add value to your processes and create a solution that integrates seamlessly with your existing systems. Using IoT technologies, we can help you collect and analyze real-time data from your machines, equipment, and devices, enabling you to identify bottlenecks, optimize workflows, and make data-driven decisions. We can also automate routine tasks, such as maintenance and inventory management, to improve efficiency and reduce costs. Our IoT-powered BPM solutions can also help you monitor and track your resources, including energy, water, and materials, enabling you to reduce waste and improve sustainability. By integrating IoT with BPM, we can help you create a more agile and responsive business that adapts to changing conditions and stays ahead of the competition. Whether you are looking to automate your manufacturing processes, optimize your supply chain, or improve your customer experience, our IoT-powered BPM applications can help you achieve your goals. Contact us today to learn more about our services for BPM development using IoT.
these are applications designed to streamline and automate repetitive tasks, reduce errors, and increase efficiency. They can help you manage everything from HR processes to financial transactions
these applications enable you to visualize your business processes, identify inefficiencies, and optimize workflows. They can help you identify bottlenecks and areas for improvement in your processes
these applications enable you to manage your digital content, such as documents, images, and videos. They can help you organize your content, ensure compliance with regulations, and improve collaboration across your organization.
these applications enable you to monitor and evaluate your business performance, track KPIs (key performance indicators), and generate reports. They can help you make data-driven decisions and identify areas for improvement.
these applications enable you to manage your interactions with customers, track sales, and provide personalized service. They can help you improve customer satisfaction, increase sales, and retain customers
these applications enable you to manage your supply chain processes, such as procurement, inventory management, and logistics. They can help you reduce costs, improve efficiency, and increase visibility across your supply chain.
these applications enable you to manage your quality control processes, track defects, and improve product and service quality. They can help you comply with quality standards and regulations, and reduce the risk of product recalls.
these applications enable you to plan, execute, and monitor your projects, track progress, and allocate resources. They can help you stay on schedule and budget, and improve project outcomes.
these applications enable you to manage regulatory compliance requirements, such as GDPR, HIPAA, or SOX. They can help you ensure data privacy and security, avoid penalties, and mitigate legal risks
these applications enable you to assess and manage risks, such as operational, financial, or reputational risks. They can help you identify and prioritize risks, and develop mitigation strategies
these applications enable you to manage your HR processes, such as recruitment, onboarding, performance evaluation, and training. They can help you improve employee engagement, retention, and productivity
these applications enable you to manage your financial processes, such as budgeting, forecasting, accounting, and auditing. They can help you ensure financial transparency, accuracy, and compliance
these applications enable you to automate your marketing processes, such as lead generation, nurturing, and scoring. They can help you improve customer targeting, engagement, and conversion
these applications enable you to manage your events, such as conferences, trade shows, and webinars. They can help you plan, promote, and execute successful events, and measure their impact.
these applications enable you to manage your sales processes, such as lead tracking, pipeline management, and forecasting. They can help you optimize your sales activities, increase revenue, and improve customer relationships
these applications enable you to manage your customer service processes, such as ticket management, service level agreements (SLAs), and knowledge management. They can help you improve customer satisfaction, reduce churn, and increase retention
these applications enable you to track your supply chain processes, such as shipment tracking, inventory management, and demand forecasting. They can help you optimize your supply chain operations, reduce costs, and improve agility.
these applications enable you to manage your physical and digital assets, such as equipment, vehicles, or software licenses. They can help you optimize your asset utilization, reduce downtime, and improve maintenance
these applications enable you to manage your logistics processes, such as route optimization, delivery tracking, and warehouse management. They can help you improve your delivery times, reduce transportation costs, and optimize your inventory.
these applications enable you to manage your product development processes, such as ideation, design, testing, and launch. They can help you bring products to market faster, reduce time-to-revenue, and increase innovation.
We are here to answer your questions 24/7
we offer BPM (Business Process Management) application development services that are designed to help our clients streamline their business processes, increase efficiency, and reduce costs. In addition to developing customized BPM applications, we also offer data analysis and reporting services to help our clients make informed decisions and optimize their processes

Based on the data analysis, we identify areas of your business processes that can be optimized or automated. We work with your team to design and implement process improvements that can help you reduce costs, improve efficiency, and increase productivity. We use BPMN (Business Process Model and Notation) to map out your processes and identify areas for improvement
We start by analyzing your business data to identify patterns, trends, and opportunities for improvement. We use various tools and techniques to collect, process, and analyze your data, such as data mining, machine learning, and statistical analysis. Our data analysts work closely with your team to understand your business needs and goals, and to ensure that the analysis is relevant and actionable
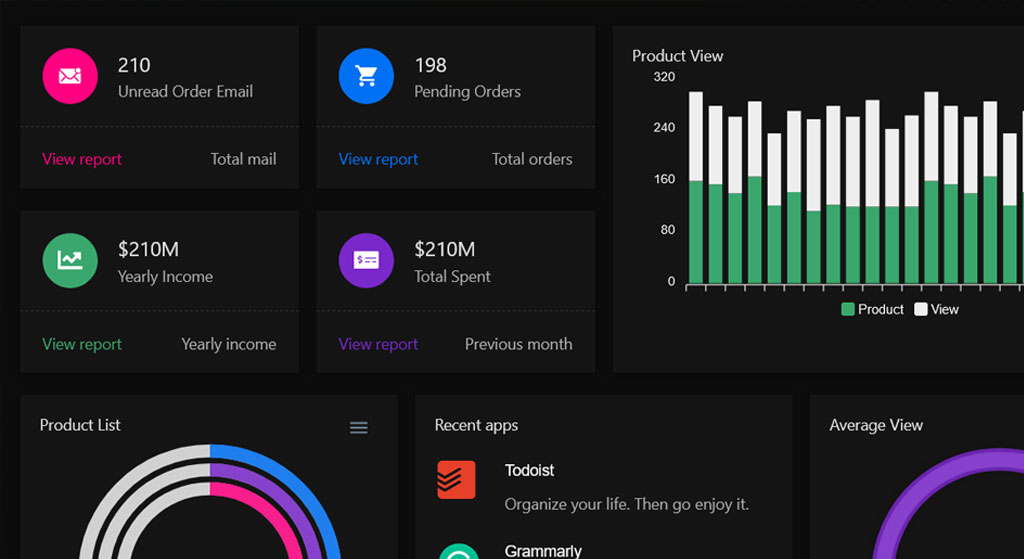
We develop customized reports and dashboards that provide real-time insights into your business processes. These reports and dashboards are designed to be user-friendly and customizable, so that you can easily monitor your KPIs, track progress, and identify trends. We use various data visualization tools such as Power BI, Tableau or Excel,

We work with your team to continuously monitor and optimize your business processes. We use a data-driven approach to measure the effectiveness of the process improvements, and to identify new opportunities for optimization. We provide ongoing support and training to ensure that your team is equipped to use the BPM applications and data analysis tools effectively
Our BPM with data analysis and reporting services are designed to help you gain a deeper understanding of your business processes, optimize your workflows, and make informed decisions. Contact us today to learn more about how we can help you achieve your business goals.
we offer BPM (Business Process Management) development services that are designed to help our clients optimize their business processes, increase efficiency, and reduce costs. In addition to developing customized BPM applications, we also offer mobile app API integration services to help our clients access their BPM data and workflows from their mobile devices.

We start by developing a customized BPM application that is designed to meet your unique business needs. We use various BPMN (Business Process Model and Notation) tools and techniques to map out your workflows, identify areas for improvement, and automate your business processes. We work closely with your team to ensure that the BPM application is intuitive, user-friendly, and scalable.
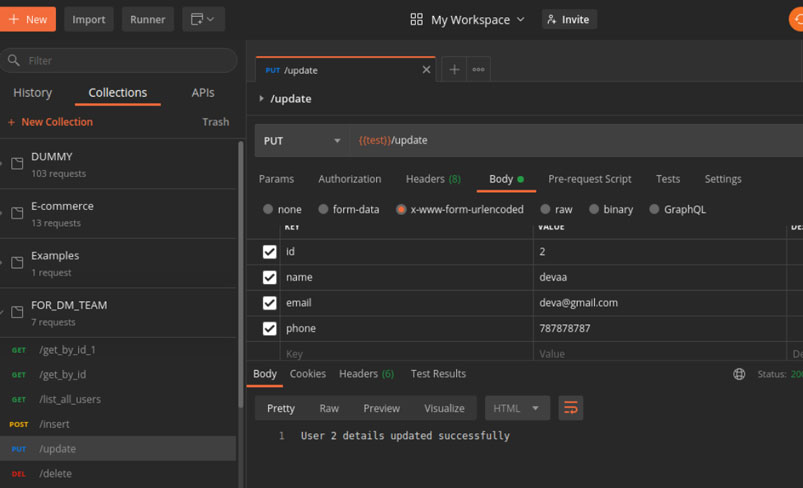
Once the BPM application is developed, we integrate it with a mobile app API that enables you to access your BPM data and workflows from your mobile device. We use RESTful API architecture to ensure that the API is secure, reliable, and scalable. We work with your team to identify the mobile app features and functions that are most important to your business, and to ensure that the API integration meets your mobile app requirements

If needed, we can also develop a custom mobile app that is designed to work seamlessly with your BPM application and API. We use various mobile app development frameworks, such as React Native or Flutter, to create cross-platform apps that are compatible with iOS and Android devices. We work closely with your team to ensure that the mobile app is user-friendly, visually appealing, and provides a seamless user experience

We thoroughly test the BPM application and mobile app API integration to ensure that they meet your business requirements and quality standards. We provide ongoing support and maintenance to ensure that the application and API are always up-to-date and secure
Our BPM development with mobile app API integration services are designed to help you access your BPM data and workflows from anywhere, at any time, and on any device. Contact us today to learn more about how we can help you achieve your business goals with our BPM development services.












BPM stands for Business Process Management. It refers to the practice of analyzing, designing, automating, monitoring, and optimizing business processes to improve efficiency, reduce costs, and enhance customer satisfaction
The benefits of BPM include increased efficiency, reduced costs, enhanced customer satisfaction, improved quality, better compliance, and greater agility. BPM can help organizations streamline their workflows, eliminate bottlenecks, and optimize their processes for maximum performance
BPM applications can help your business by automating repetitive tasks, simplifying complex processes, improving collaboration, enhancing visibility, and enabling real-time monitoring and analysis. BPM applications can also help you identify areas for improvement, track progress, and measure performance.
We can develop various types of BPM applications, such as process automation, workflow management, document management, quality management, compliance management, and customer relationship management. We can also develop customized BPM applications that are tailored to your unique business needs.
Our development process for BPM applications involves several stages, including requirements gathering, analysis and design, development and testing, deployment, and support and maintenance. We use agile development methodologies to ensure that the application is delivered on time and within budget.
We use various technologies for BPM application development, such as BPMN (Business Process Model and Notation), RESTful APIs, cloud computing, machine learning, and data analytics. We choose the technology stack based on your specific business requirements and preferences
We take security very seriously and use various measures to ensure the security of your BPM application, such as role-based access control, data encryption, secure coding practices, and regular security testing and audits. We also comply with industry standards and regulations, such as GDPR and HIPAA, if applicable.
We offer various support and maintenance services for BPM applications, such as bug fixing, performance tuning, feature enhancements, and security updates. We provide 24/7 technical support and ensure that your application is always up-to-date and running smoothly
Initiate your journey by seeking a complimentary consultation for your digital transformation. Our team is prepared to offer comprehensive guidance, ensuring the success of your project.

